Create Group Policy to Whitelist Applications
Create Group Policy to Whitelist Applications – Ransomware prevention
Go to https://java.com/en/download/
Take note of the latest Java Version (eg, 8u301)
Login to your to a server that can Access/Create/Edit Group Policy objects
Open the run command, type in gpmc.msc – Click OK
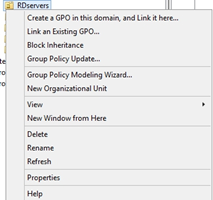
Right click on the Organizational Unit you wish add the Whitelist to, Select the first option.
(Create GPO)
Enter a name for the Whitelist, Click OK (i.e CryptoLocker/Ransomware Prevention)
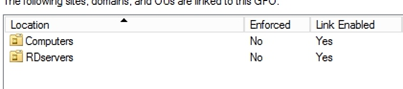
Link the newly create GPO to any other Organizational Units you want to be added to the GPO.
(eg. Right click on Computers OU, ‘select Link an Existing GPO…’ then select the new GPO)
Right click on the GPO, click Edit…
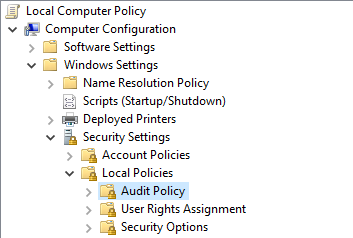
Drill down in; Computer Configuration >> Policies >> Windows Settings >> Security Settings >> Software Restriction Policies
Right click on Software Restriction Policies, Select the first option

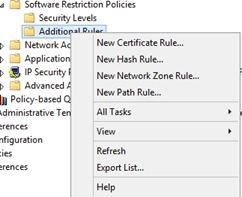
Right click on Additional Rules, Select New Path Rule…
Enter the following path: %localAppData%\*\*.exe
Security Level = Disallowed
Click OK

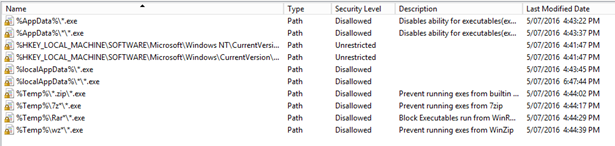
Create Additional Path Rules for the following paths:
%localAppData%\*.exe
%AppData%\*.exe
%AppData%\*\*.exe
%Temp%\*.zip\*.exe
%Temp%\7z*\*.exe
%Temp%\Rar*\*.exe
%Temp%\wz*\*.exe
Your list should look like this:
Exit out of Group Policy Editor.
Create another GPO called Cryptolocker/Ransomware – Whitelist Allow (Link to same OU’s as previous GPO)
Right click on the GPO, click Edit…
Drill down in; – Computer Configuration >> Policies >> Windows Settings >> Security Settings >> Software Restriction Policies
Right click on Software Restriction Policies, Select the first option

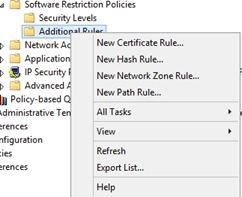
Right click on Additional Rules, Select New Path Rule…
Under ‘Path:’ enter the path of the Java Installer you wish to allow:
%localappData%\temp\jre-8u301-windows-i586-iftw.exe
Set Security Level to ‘Unrestricted’
Enter an appropriate description name.
Click OK.

Verify that new Path Rule has been added to Whitelist.
Close GPO Editor.
Refresh Group policy Management
Go down to the Whitelisting Çryptolocker/Ransomware – Whitelist Allow GPO, click on it once
In the window on the right select ‘Settings’ from the tabs.
Drill down to; Computer Configuration >> Policies >> Windows Settings >> Security Settings >> Software Restriction Policies/Additional Rules
Verify that new Path rule is shown in Policy List.
Exit Group Policy Management.
Go to a machine what is linked to the GPO to test whitelist.
Run Java Updater/Installer
Note the successful installation of Java
If fails = Perform forced Update to GPO
From Administrative Command Prompt,
gpupdate /force